By ffurnari
Changes in how some access the “Y” Drive
On Tuesday June 30 we will change the way some people access the BUMC file server (the “Y” drive). If you currently access the “Y” drive using the path that begins with \\bumc.bu.edu\bumc\ on a PC or smb://bumc.bu.edu/bumc/ on a MAC, you will need to correct the way you connect to the server. You will now want to connect using \\filesrvs.bumc.bu.edu\bumc on PC or smb://filesrvs.bumc.bu.edu/bumc on a MAC. Please visit our mapping the Y drive page for detailed instructions.
We are making this change to make it easier for some to access the BUMC website. Currently to access the website you need to type in www.bumc.bu.edu into the address bar, after the change is in place, the www won’t be needed and simply using bumc.bu.edu will work.
BUMC IT Welcomes Yoal Peguero
Yoal Peguero joined BUMC IT in January as our newest Client Support Specialist. Yoal graduated from BU in 2013 earning his BS in Health Science with a minor in Public Health. While a student at BU he worked in CAS IT as a computer assistant. Our colleagues at CAS IT spoke highly of Yoal and his work. Yoal worked at Brigham and Women’s Hospital in alumni communications where, among other things, he oversaw their website. Most recently, he worked down the street at Boston Public Health Commission as a program coordinator.
Yoal fills the position vacated by Lloyd Rolles who was promoted to Computer Support Specialist. Lloyd filled the position vacated by James Lau who is now a Systems Application Administrator.
Resolved – Echo360 Classroom Recording Service is unavailable
IS&T teams have resolved the incident with vendor assistance.
Please note: The feature used for scheduling recordings remains unavailable while IS&T teams and the vendor are determining the root cause of this issue.
Echo360 service is intermittently degraded or unavailable. Clients will be unable to schedule recordings and may have difficulty viewing existing recordings. Please check TechWeb for updates.
Welcome, Scott Wilson!
BUMC IT Client Services is proud to welcome Scott Wilson starting as a Computer Support Specialist today. Scott graduated from Wentworth Institute of Technology with a BS in Computer Networking in 2012 and recently worked for TMNG Global as a Network and Desktop Support Specialist. Scott brings extensive Windows and Mac experience to our team.
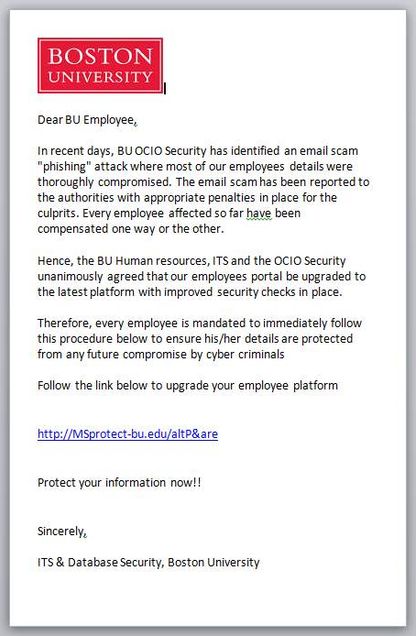
The phishing scammers are at it again!
As described last week in a BU Today article, members of the BU community were recently victims of phishing; and IS&T has again received several reports of a phishing message being received by members of our community like the one below.
We believe the scammers are trying to use the fact that they were successful last time to continue and extend their crime. The message to watch out for claims to be from BU Security and talks about protecting you from the evils of phishing. You can tell the message is a fake because it claims to be from BU, and even uses the BU logo, but it is pointing you to a link that is not a bu.edu link.
A real BU link will always have “ .bu.edu/ ” in it. There is always a dot before bu and a slash after edu, as shown below.
Other things to watch out for:
- If you are prompted to Web Login, make sure it is the authentic BU Web Login page which begins with https://weblogin.bu.edu/something
- Remember that BU will NEVER ask you for your password or ask you to “verify” it; nor would any other legitimate business or institution. It is important that you safeguard your passwords and never give them to anyone.
For more good ways to detect phishing, go to: www.bu.edu/infosec/howtos/how-to-detect-phishing/.
Additional information on phishing is provided by IS&T at www.bu.edu/tech/phishing.
Making your spam/phishing filter more effective
Mail that is clearly spam is filtered for you, automatically. However, one person’s spam might be another person’s research project, so other messages are simply tagged as suspicious and then allowed to go through. You can decide how to handle suspicious mail that does get through, following the tips for Managing Spam provided by IS&T at www.bu.edu/tech/comm/email/unwanted-email/spam/.
Report phishing
If you see a phishing message, please send it and full headers to abuse@bu.edu. For details on how to do this, see www.bu.edu/tech/comm/email/unwanted-email/report-abuse/.
Welcome Lloyd Rolles!
Please join us in welcoming the newest member of our Service Desk Team, Lloyd Rolles. Lloyd graduated BU this May with a BS in Health Sciences from Sargent College. He was most recently working as a casual employee splitting his time between Student Health Services and the IT Help Center where he supported faculty, staff, and students on both the academic and clinical sides. He brings not only troubleshooting knowledge but also knowledge of BU systems as well as experience in the Service Now ticketing system.
Welcome Myriam Bikah
Myriam Bikah joins BUMC IT today in the position of BI Developer II. Myriam joins BU after spending the past 5 years with the American Association of Community Colleges (AACC) in Washington, D.C., as a Data and Research Associate. There she helped colleges understand student achievement measures and trends, in part by developing MicroStrategy dashboards and OLAP reports, creating data dictionaries and training videos. Prior to the AACC, Myriam worked at the National Committee for Quality Assurance (NCQA) as a Heath Care Analyst, translating healthcare performance measures into SAS specifications, and performing extensive statistical analyses of healthcare data. She holds an MS in Industrial Engineering from the University of Nebraska – Lincoln, and a BS in Mathematics from UNC Charlotte. Her thesis work involved the design of a user-centered, portable, ergonomic, real-time, solid-state neutron detection device for Homeland Security applications (related work here). She’s as fluent in calculus as she is in French. Myriam is new not just to BU, but also to the city of Boston. Welcome, Myriam!
Upgrade to BUMC VPN starting July 25
On July 25, 2013 we will be releasing an upgrade of the Cisco AnyConnect VPN clients for Windows, Mac, and Linux. After July 25 any login to VPN will automatically upgrade to the new version. The current version has vulnerabilities that could be exploited as well as an expired application certificate that might give errors during installation when new clients connect to the VPN for the first time. A few things to note about this upgrade:
- The Windows interface is unchanged and will look similar to the previous VPN client.
- The Mac version has changed and now mimics the Windows version. The functionality will be virtually the same, but the look and feel of the application interface has changed.
- The VPN client is now branded with BU logos within the user interface.
- For advanced VPN users, we have enabled population of VPN endpoints in the client's drop down list. If you login to multiple groups to connect to several applications (for example work2.bumc.bu.edu/Slone), you will notice that the drop down list will automatically populate with the names of the different groups that you login to after you connect to them for the first time. From that point on you can select the group from the pull down instead of typing it in each time you connect.
If you have any questions or concerns about this VPN upgrade, please contact email The BUMC IT Helpdesk or call us at 617-638-5914.
Centrally Funded Computer Support Begins July 1
Over the past few months BUMC Information Technology has been enrolling departments into a new support structure that is centrally funded by the schools, initiated by Provost Antman and Bobby Sprinkle, Executive Director, BUMC IT. Starting July 1 this new support structure officially begins for BU departments on the Medical Campus. As part of this process, we will be doing an inventory of computer equipment that has been purchased with BU funds (either departmental or grant). Once a department is fully inventoried it will no longer be charged for setups, hourly support, or annual support agreements, but will be centrally funded by Medical Campus schools. For more information about this program or questions feel free to visit or call BUMC IT https://www.bumc.bu.edu/it/support/subscription/centrally-funded-desktop-support/
Secure Paper Shredding June 13
BUMC IT and BU IS&T Information Security will be sponsoring a paper shredding day, Thursday, June 13 from 10am to 1pm along the Talbot Green. Bring any work related or personal documents that you would like to have securely shredded on site at the shredder truck. We will also have an area nearby where you can drop off computer equipment you would like recycled as well as hard drives you would like destroyed.